about : Upload
Drag and drop your PDF or image, or select it manually from your device via the dashboard. You can also connect to our API or document processing pipeline through Dropbox, Google Drive, Amazon S3, or Microsoft OneDrive.
Verify in Seconds
Our system instantly analyzes the document using advanced AI to detect fraud. It examines metadata, text structure, embedded signatures, and potential manipulation.
Get Results
Receive a detailed report on the document's authenticity—directly in the dashboard or via webhook. See exactly what was checked and why, with full transparency.
Understanding Common Signs of a Fake PDF
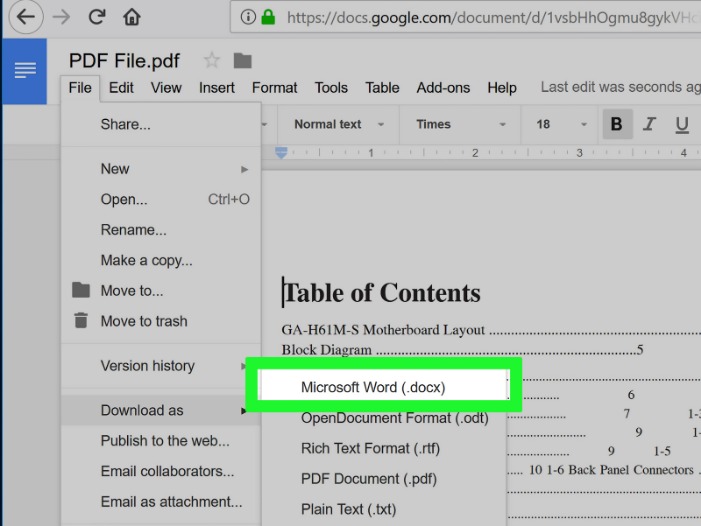
Detecting a counterfeit PDF often begins with observing subtle but consistent red flags. A suspicious document may contain inconsistent or missing metadata such as creation and modification timestamps that do not match the claimed timeline, or author fields that are blank or use generic names. Text anomalies are another giveaway: look for inconsistent fonts, uneven line spacing, invisible characters, or sudden changes in formatting that indicate content was pasted from different sources. OCR (optical character recognition) errors can create odd spacing and garbled characters when text has been scanned and re-saved, which may reveal layers of editing.
Visual elements also betray manipulation. Images with mismatched resolution, unexpected compression artifacts, or duplicated logos suggest elements were copied and inserted. Check for inconsistent alignment, margins that suddenly shift, or page numbers that have been altered. Signatures and stamps deserve special attention: an authentic embedded signature should be verifiable via a certificate chain or signature metadata; a pasted image of a signature without associated cryptographic verification is easily forged. Watermarks or digital seals that appear low-resolution or display color mismatches are often signs of tampering.
Technical inconsistencies such as broken hyperlinks, missing fonts, or suspicious JavaScript embedded within the PDF can also indicate malicious modification. Many fake documents rely on manual edits that leave behind artifacts—comments, revision history, or hidden form fields—that can be uncovered with a careful inspection. Recognizing these common signs establishes a baseline for further automated and forensic checks, and helps prioritize documents that need deeper analysis for potential fraud.
Technical Methods to Verify Authenticity
Beyond visual inspection, reliable detection of fake PDFs uses technical methods that analyze both content and structure. Start with the metadata layer: extract creation, modification, and producer fields and compare them with expected values. Tools that perform byte-level analysis can reveal whether a file contains appended content, multiple embedded files, or suspicious streams that do not match the declared format. Hash comparisons against known originals or version histories quickly show whether a file has been altered since its last legitimate save.
Cryptographic verification is a critical step for legally significant documents. A digitally signed PDF should include a cryptographic signature and an associated certificate chain tied to a trusted authority; validating signatures against trusted root certificates confirms that the document has not been altered since signing. For unsigned documents, automated consistency checks—like comparing text extracted by OCR to visually rendered text, or validating embedded fonts and images against expected sources—help detect substitutions and manipulations. Heuristic and machine learning models can flag anomalies in language patterns, layout, and image properties that are statistically unlikely for authentic documents.
For organizations that need scalable verification, integrating APIs and pipelines is essential. Cloud connectors to storage services and automated webhooks enable continuous monitoring and reporting. When manual review is necessary, a layered approach that combines automated results with expert forensic analysis gives the best outcome. For those looking for a start, specialized services and tools that detect fake pdf provide rapid analysis and transparent reporting so suspicious files can be triaged efficiently and escalated when warranted.
Real-World Examples, Case Studies, and Best Practices
Real incidents underscore the importance of robust PDF verification. In one case, a forged contract circulated with an authentic-looking corporate logo and signature image; routine checks caught mismatched metadata and a certificate chain that did not correspond to the purported signer. Another example involved altered academic transcripts where page-level image edits were used to change grades; pixel-level comparison and font analysis revealed that certain characters had been replaced rather than retyped. In both scenarios, combining visual inspection with technical validation prevented costly acceptance of fraudulent documents.
Organizations benefit from defined workflows and best practices. Implement a standardized intake process requiring initial automated checks—metadata extraction, signature validation, and image integrity scans—followed by escalation rules for any anomalies. Maintain a repository of verified originals and versioned documents to enable quick hash comparisons. Train staff to recognize obvious red flags and ensure that legal and security teams have access to forensic tools when deeper analysis is needed. Periodic audits of document handling procedures reduce risk and improve response times.
Integrating detection into everyday operations also reduces friction. Use secure upload portals, require digitally signed submissions where possible, and log every document transaction to create an audit trail. When dealing with external partners, establish verification requirements and share accepted certificate authorities to avoid ambiguity. Combining technical solutions, clear policies, and continuous education creates an environment where fake PDFs are identified and mitigated before they cause harm.