PDF files are convenient, portable, and widely trusted, which makes them an attractive vehicle for fraud. Criminals and opportunistic actors exploit the perceived immutability of PDFs to circulate counterfeit invoices, manipulated receipts, and altered documents that can deceive finance teams, suppliers, and consumers. Learning how to spot anomalies rapidly and reliably is essential for preventing financial loss and preserving business reputation. This guide explains common fraud techniques, technical verification methods, and real-world practices to detect fake pdf and related document fraud with clarity and confidence.
Understanding Common PDF Fraud Techniques and Red Flags
Fraudsters use a range of techniques to make a fraudulent PDF look legitimate. Typical methods include editing existing documents to change amounts or dates, substituting logos and supplier details, exporting screenshots of invoices to avoid searchable text, and embedding manipulated images to mask alterations. Social engineering is often paired with these technical tricks: urgent payment requests, altered bank details, or spoofed supplier email addresses add pressure that bypasses standard checks. Recognizing behavioral and visual red flags is the first line of defense.
Visual indicators include inconsistent fonts or spacing, low-resolution logos that look pixelated when zoomed, mismatched currency symbols, and formatting that differs from known templates. Metadata inconsistencies can also reveal manipulation: creation dates that don’t match claimed issuance dates, or author fields that point to consumer tools rather than corporate systems. Technical flags include non-searchable text where searchable text is expected, unusually large embedded images, or missing digital signatures.
Operational red flags arise from process deviations: invoices submitted off-cycle, sudden changes in supplier banking details without prior notice, or requests to expedite payment via nonstandard channels. Combining visual inspection with process controls reduces risk. For automated help, tools and services exist to detect fake invoice and scan for subtle alterations across files, making it easier to prioritize suspicious items for human review. Training staff to question deviations and to use verification tools consistently is critical for reducing success rates for attackers trying to detect pdf fraud opportunities.
Technical Methods to Verify the Authenticity of PDFs
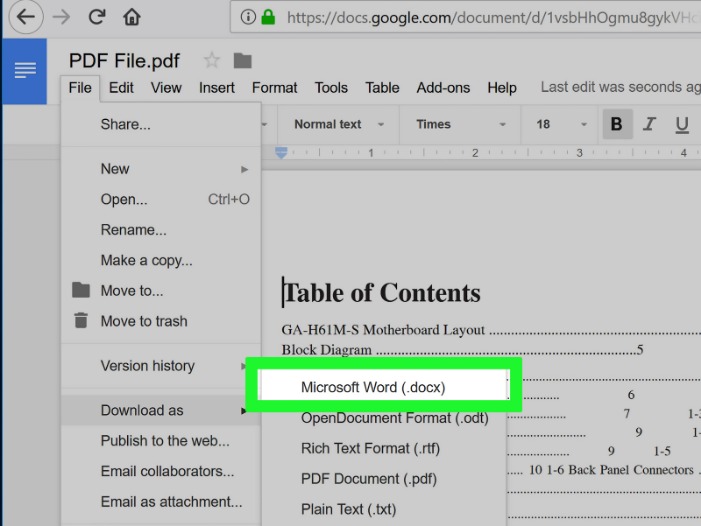
Technical verification provides objective evidence that a PDF has been altered or is forged. Start with file metadata: examine creation and modification timestamps, application identifiers, and embedded author strings. If the metadata shows a modified date later than the claimed issuance or an author that indicates consumer software rather than an accounting system, that is suspicious. Digital signatures are one of the strongest defenses. A valid digital signature ties the document content to the signer and shows whether content changed after signing. Verifying the certificate chain and timestamping ensures the signature was valid at the time of signing.
File hashing and checksums provide a binary-level integrity check. If an organization stores hashes of issued invoices, a mismatch between the stored hash and the presented file signals tampering. Optical character recognition (OCR) can uncover when an invoice is an image-only file: genuine system-generated invoices are usually text-based and searchable. Image analysis tools can detect clone stamping, inconsistent compression artifacts, or signs of cut-and-paste editing in logos and tables.
Forensic-level inspection includes layer and object inspection within the PDF structure. PDFs can contain multiple layers, hidden objects, or embedded fonts that mask alterations. Specialized utilities can flatten layers, extract embedded images, and list form fields or JavaScript embedded in the file—malicious scripts or hidden form fields are indicators of sophisticated fraud. Combining these technical methods with process verification—contacting the supplier via known channels, confirming bank account changes by phone—creates a robust multi-factor approach to detect fraud in pdf files.
Practical Steps, Case Studies, and Best Practices for Organizations
Organizations that have successfully reduced losses from fake documents use layered controls: prevention, detection, and response. Preventive measures include standardized invoice templates with unique identifiers, strict supplier onboarding with verified bank details, and locking down approval workflows so invoices cannot bypass required sign-offs. Detection measures combine automated scanning (for metadata, digital signatures, and content anomalies) with manual checks for out-of-band confirmation. Response plans define who investigates, how suspected fraud is quarantined, and how affected parties and banks are contacted to halt payments.
One case study involved a mid-sized company that received an invoice that visually matched a regular supplier but had altered bank details. Automated tools flagged metadata inconsistencies and a missing digital signature; a quick phone call to the supplier confirmed the attempted fraud. Because the company stored payment approval hashes and required two-person verification for bank changes, the payment was stopped and the fraud attempt documented for law enforcement. Another retailer detected a pattern of low-value fake receipts that abused return policies; image analysis showed identical compression artifacts across multiple receipts, revealing a single source generating the forgeries.
Best practices include maintaining an auditable archive of issued invoices and receipts, using digital signatures for critical documents, implementing dual-control approvals for payments, and training procurement and accounts payable teams to recognize social engineering tactics. Regularly running scans to detect fake receipt and audit trails helps uncover anomalies early. When paired with clear escalation procedures and forensic-capable tools, these steps make it significantly harder for fabrications to succeed and faster to remediate when they appear.